Have you ever seen an email from your CEO asking you to redeem a voucher worth AED 3,000 or to share your login details for an urgent IT-related problem? Or was it an email asking you to urgently help to access a website link to fill out a form? As it turns out, you’ve been phished.
Phishing attacks – known as deceptive emails aimed at tricking users into divulging sensitive information or spreading malware – represent a perpetual menace to organisations and individuals alike. Today, phishing attacks are becoming more advanced and difficult to identify than ever before, with a little help from Artificial Intelligence (AI).
A Looming Concern
Recent data from the UAE underlines the urgency of the matter: the majority of organisations have fallen victim to email-based phishing attacks. A staggering 86 percent have encountered attacks which have unfortunately been successful at obtaining access to their data, with nearly half of these incidents resulting in direct financial losses. These sobering statistics highlight the critical need for strategies that not only address the vulnerability of contemporary IT infrastructures but also proactively deter these malicious attempts.
The sheer ubiquity of phishing attacks cannot be understated. It is estimated that globally a staggering 1 in every 100 emails harbors malicious intent, with an estimated 3.4 billion spam emails sent every day. This sobering reality amplifies the urgency of the situation. Organisations must embrace a paradigm shift to combat phishing effectively, transcending traditional security measures that are increasingly rendered obsolete by the rapidly evolving tactics of cybercriminals.
The AI Factor: Reinventing cyber attacks
We know that threat actors are getting better at disguising phishing attacks, with entire criminal organisations dedicated to building services like phishing-as-a-service for other cybercriminals to use in their targeted phishing campaigns.
One of the ways in with these threat actors are becoming more advanced is by adopting Artificial Intelligence (AI) to aid in the development of cyberattack campaigns, with services like WormGPT (a generative AI tool for bad actors similar to ChatGPT) that allow adversaries to launch sophisticated phishing and business email compromise attacks with relative ease.
These malicious AI tools use the latest marketing and branding from your websites and learn from previously successful phishing campaigns to create highly accurate phishing campaigns that can evade even the most trained eye from identifying the phishing email.
It is well noted amongst security professionals that AI-generated phishing emails have a higher opening rate than humanly drafted emails, as they’re more proficient with creating identical copies. And when using ChatGPT, sensitive data is leaked due to employee unawareness and negligence inputting said data into the models to generate content, aiding the phishing attacks to be more customised. Earlier this year, Samsung joined a growing list of tech companies that are banning the use of Generative AI, most prominently ChatGPT, amongst their employees. This is fueled by the tracked data leaks noticed by their IT teams. While other giants, like Amazon, are warning staff to be more vigilant with the type of data shared with these open GPT models.
Reinforcing the Resilience with Zero Trust’s Ascendancy
As technology’s inexorable march continues, the synergy between innovation and vulnerability persists. In this era of escalating cyber threats, the approach to cybersecurity must evolve with equal fervor. Pausing the use of Generative AI technology can only be considered a temporary solution, seeing as the popularity of AI is only going up from here. Many experts are still holding AI as being the leader of technological evolution in the coming decade.
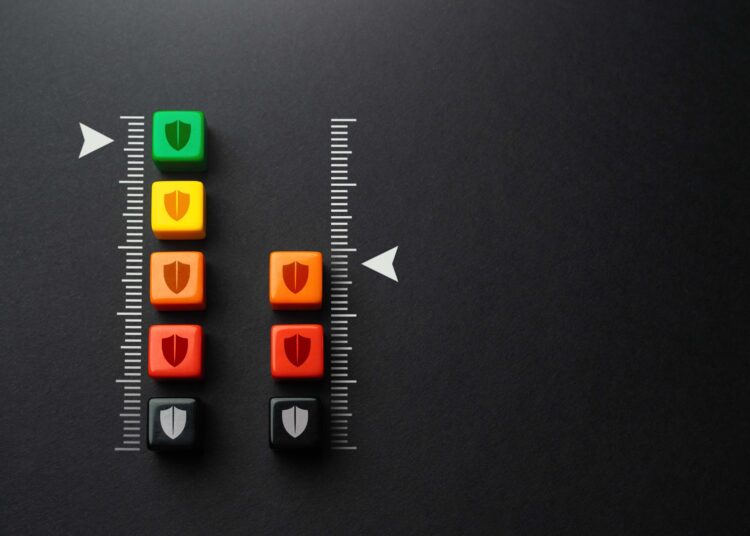
So, how can organisations use AI to their advantage? The concept of ‘Zero Trust’ holds the solution to these concerns. Zero Trust advocates for the continuous verification of users and devices, challenging the traditional notion of implicit trust within networks. This proactive approach has become increasingly vital as organisations face a persistent menace: phishing attacks.
Leveraging the power of artificial intelligence (AI), organisations can further enhance their Zero Trust frameworks against these evolving threats in several ways. Organisations can leverage AI to their advantage, using AI models to detect anomalies within their identities (oversubscribed users / endpoints, continuously out of compliance devices and users that trigger risk thresholds on a continuous basis) and automatically change access for those users or devices, restricting access to an isolated network segment or to quarantine them with limited to no access to resources and data until remediation actions are taken.
In addition, AI can help with identifying anomalies in contextual information such as behavioral biometrics, velocity, time-of-day/day-of-week and other inputs during authentication and authorisation to continuously evaluate the risk level of every single identity that is accessing resources and data, while taking the necessary action of enforcing step-up authentication requiring the user to authenticate using a different two-factor authentication mechanism or to block the user/device from accessing any resources until corrective action is taken.
AI driven real-time threat mitigation, data encryption, adaptive security policy and risk based engines, real time threat intelligence, further enhance organisations’ ability to combat threats such as phishing effectively.
Protecting against the threat: Organisational awareness
A holistic approach calls for human expertise at the centre of it all, meaning organisations need to weaponise their IT teams with top-grade tools. Out of many such tools, Phishing-resistant MFA involves high assurance authentication with the use of cryptographic keys and digital certificates, as well as requiring the physical proximity of the user to the device from which they are requesting access to a resource. There are a few passwordless MFA options that offer phishing-resistance, namely FIDO2 keys, passkeys, and certificate-based authentication with Bluetooth proximity detection.
Certificate-based authentication (CBA) is considered the highest assurance of these options. It involves the use of verified digital certificates assigned to a user and devices from which a user authenticates themselves, along with a Bluetooth proximity requirement. This ensures the user is in close physical proximity to the device from which they are accessing a resource and that the device itself is also a trusted device with a known valid digital certificate assigned to it by a certificate authority.
In conclusion, the intertwining of phishing attacks and AI that can be used in nefarious ways underscores the pressing need for innovative strategies to combat cyber threats. As organisations grapple with the aftermath of successful phishing attacks, it becomes evident that traditional security paradigms fall short. Zero Trust offers a compelling solution by challenging assumptions, leveraging advanced technologies, and presenting a holistic blueprint for defense.
By adopting a proactive stance that embraces continuous verification, adaptive policies, and AI-driven insights, organisations can emerge from the fray with enhanced resilience and security, effectively countering the menace of phishing attacks. In this dynamic landscape, where adversaries are quick to adapt, the Zero Trust approach stands as a sentinel, vigilantly guarding against the tides of digital malevolence.









Discussion about this post